by Ian Matthews Update April 1, 2007
WHAT IS USER ACCESS CONTROL (UAC)?
User Access Control is likely the most controversial new feature in Windows Vista. In addition to beta testing Vista since Beta 1, I have attended several MS sponsored webinars, read Microsoft white papers and asked MS staffers many direct questions. The purpose of this article is to distill the information into a brief.
Since the Windows NT days, Microsoft has (correctly) told everyone that they should log into their PC’s with Standard User (i.e. non-Administrator) account and we all know we should, but no-one does. The problem is that if you are logged in as an Admin and some malicious software is loaded, it does so with full system permissions. So MS developed a “Least Privilege” model called User Access Control, primarily provides two features:
1: ARE YOU SURE?
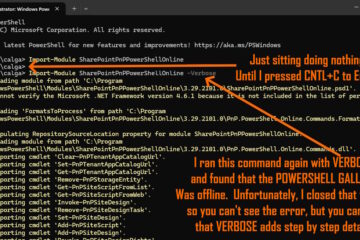
Vista Administrators are assigned a Standard User token when they log in; if they need to do something that requires administrative privilege (such as deleting a file or installing a program) they are prompted to elevate their privilege which grants them a real administrative token for the task. If a Standard User attempts to do something requiring Admin privilege, they are prompted for administrator credentials. The problem is that the number of times you are prompted with the proverbial “Are you sure” popup is staggering for all but the most modest users.
Unlike nearly all of the other ads in the series, Apple accurately lampooned PC limitation in this MAC vs PC advert:
Of course Apple couldn’t get through a whole ad. without stretching the truth. In this case they insinuate that if you disable UAC, Vista becomes wide open with no security. Of course, this is completely inaccurate. UAC is not related to firewalls, popup blockers, anti-spam/anti-phishing in Mail, or dozens of other security measures in Vista.
Perhaps the most annoying part of this Least Privilege concept is that you can not preauthorize applications. I have a corporate user who needs to update for a particular piece of scientific software on a weekly basis. Under Windows 2000 and XP, I simply gave this “restricted user” full read/write NTFS permission to the programs install directory. Under Vista, the download application fails because UAC sees the app trying to connect to the internet and pops up asking for Admin credentials. There is no “check box” or registry entry I can make to stop UAC from asking about this application and forcing Admin credentials. I have confirmed with Microsoft that there is also no Domain Group Policy or other process I can follow to authorize this application. So I have a dilemma:
- if I provide the user with local admin user and password, I completely lose control of that box.
- if I disable UAC, I lose its benefits
I’m not happy and a bit mystified how this obvious feature made through all the beta’s and RC’s without being implemented. The research firm Gartner Group said that UAC will drastically slow the adoption of Vista in the corporate space. Preauthorization must be something Microsoft are working on for Vista’s SP1, but after dozens of conversations with various levels of Microsoft support, I still have no official confirmation that they even see this as a problem.
In addition to this popup “are you sure” madness, is something many power users will not be aware of called Virtualization:
2: VIRTULIZATION
UAC “virtualizes” x:\PROGRAM FILES; x:\WINDOWS and parts of the Registry using a “Copy on Write” logic. This is a messy business. Under UAC there it is not possible to have standard users write to any file or folder under x:\PROGRAM FILES (if you set the NTFS permissions to EVERYONE, FULL CONTROL, users still are unable to write to that location… VERY frustrating). The logic is that users should NEVER write to the same location programs or critical system files are stored. When a user launches an application, all is well but when they need to change something (say something simple, like an .INI file that keeps track of their current settings), the file will be copied (“virtualized”) to x:USERS\<username>\AppDataLocalVirtualStoreProgram Files\<appname> . This means that you may have many duplicated (but different for each user) files stored in each user profile as well as the original location. This can can a crisis, take my story as a cautionary tale:
I wrote my own bookkeeping software and put both application software and data files into x:\PROGRAM FILES\UR_BOOKKEEPING\. I wrote this code very quickly 5 years ago and periodically the database I write to corrupts, so I also wrote a small utility to fix that database. Under all previous versions of Windows this has worked just fine. Vista however, had “virtualized” my database file to a location under x:\USERS but my repair code was set to look a x:\PROGRAM FILES. Imagine my surprise when my repair utility told me all was well. After I turned off “virtualization” (see below), my virtualized files were moved back to x\PROGRAM FILES\UR_BOOKKEEPING and my repair until functioned as expected. This was not a fun experience.In a bizarre twist, Adobe Acrobat 8 will not easily install in Vista if UAC is disabled. The solution is to run the Adobe setup routine from the expanded download files. Click HERE for details.
HOW TO DISABLE or CONTROL UAC
User Access Control (UAC) can easily disabled outright or granularly controlled. This is a nice change from the Vista Beta’s, where manual registry changes were required to effect change. MS is expecting many people and most corporations to disable this feature outright.
Disable UAC: START, CONTROL PANEL, USER ACCOUNTS, DISABLE USER ACCESS CONTROL:

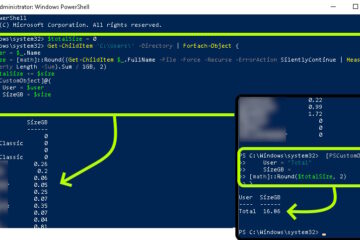
Control UAC: START, CONTROL PANEL, ADMINSTRATIVE TOOLS, LOCAL SECURITY POLICY, LOCAL POLICIES, SECURITY POLICIES, scroll to the bottom
![]()
The notion software should have its user files saved in some location other than x:\PROGRAM FILES is well known in the developer community and I think the logic has some merit. The problem is that almost no-one, including Microsoft adheres to it. Vast amounts of software will NOT function correctly with UAC enabled, including major corporate programs from Microsoft like Dynamics GP (Great Planes). For the record MS says they are developing patches for all of their software but the cost of integrating all those patches could easily exceed the business value of UAC.
After extensive testing in both personal and corporate environments, I have given up on UAC… for now. It is a great concept that just is not practical in corporate environments. Perhaps after Service Pack 1 for Vista is released, it will be better.
For more information try these:

0 Comments