In the simplest terms, Device Guard is a new Windows 10 optional feature that controls access to boot processes and memory while also blocking any software that is not specifically approved (like a whitelist).
Windows Device Guard is actually a set of three features:
- Platform and Secure Boot locks down boot processes by requiring ‘UEFI Secure Boot Mode‘ which ensures the UEFI firmware is digitally signed and therefore all but guarantees it has not been tampered with.
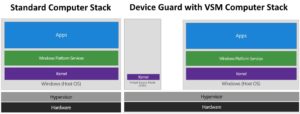
. - Virtual Secure Mode (VSM) turns on core HyperV components to allow Windows to isolate each application’s memory.
. - Configurable Code Integrity (CCI) allows only programs that an administrator approves.
ISSUES WITH DEVICE GUARD:
- CCI requires administrators to figure out all of the applications that are in use inside a company and then add those program SHA256 hashes into a Group Policy or MDM.
. - CCI does this using digital signatures so applications that do not have digital signatures can not even be considered for this and that limitation.
. - VSM needs a CPU that supports virtualization (nearly all corporate grade CPU’s since about 2010)
. - Secure Boot requires UEFI to be in native mode, not mixed or compatibility mode
Very few companies will implement this Device Guard (and its sister Credential Guard) technology because while the tech it self is easy enough to turn on and configure, it is time consuming, inflexible and very difficult to get right. I expect Device Guard to be used in very high security environments with a limited set of infrequently changing applications, like the military (think field hardware) and banks (think ATMs).
For all the details on Device Guard and Credential Guard and how to implement them, see this very nicely written Microsoft article.

1 Comment
SOLVED: What is Windows Credential Guard - Up & Running Technologies Calgary · December 21, 2017 at 11:44 am
[…] to allow Windows to isolate each application’s memory. The graphic to the right mentions Device Guard but operates the same for Credential […]