 A Whaling Attack is an attempt to take information or money from a high net worth individual or senior executive. Whaling Attacks are in the phishing spectrum as follows:
A Whaling Attack is an attempt to take information or money from a high net worth individual or senior executive. Whaling Attacks are in the phishing spectrum as follows:
| Whaling Attack | Spear Phishing Attack on high value individuals or executives |
| Spear Phishing Attack | Targeted attack on you to collect information about you |
| Phishing Attack | Attack looking for information on you but sent to many |
| Mass Attack | Old style spam not targeted at any one individual |
 At the lower end of the spectrum these attacks are nearly always completed through simple emails. At the higher end of the spectrum, sophisticated techniques like Doxing are used in which often low paid workers often in the third world spend a week or more researching their target. In addition to all of the obvious sources of incormation (Twitter, Facebook, corporate websites, blogs) these doxers will:
At the lower end of the spectrum these attacks are nearly always completed through simple emails. At the higher end of the spectrum, sophisticated techniques like Doxing are used in which often low paid workers often in the third world spend a week or more researching their target. In addition to all of the obvious sources of incormation (Twitter, Facebook, corporate websites, blogs) these doxers will:
- call the employer and say that they have a complaint about their target so they need to know their managers name and contact information
- call children and ask (or sometimes even demand) information like siblings names, birthdates, addresses…
- call schools and ask for transcripts
- call parents or siblings indicating that the victim has been involved in an accident (to add time pressure) and request private details (like Social Insurance Numbers and health information)
- setup ‘honey pots’ which are simple fake websites that match a victims hobby then invite that victim to join (because most people use their corporate username and password on private websites)
- contact credit agencies to pull reports
- read annual reports for details about an individual
For just a few hundred dollars, a hacker can be given a dossier containing thousands of important personal details that they can then use to trick you into given them more. For instance, a common whaling attack involves tricking the target into providing corporate credentials thereby allowing the hacker to get inside your company network, steal corporate secrets or request large fund transfers.
If you are a ‘whale’, you are likely a CEO, CFO, COO, on a notable Board of Directors, or famously wealthy (celebrities, lottery winners…) and you need to be careful. You should skim through our short explanation of how hackers get your passwords.
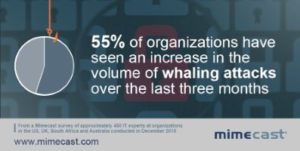
Whaling attacks have been on the rise since 2014 but in 2017 really took off.



1 Comment
SOLVED: Windows Computer Browser Service is Disabled or Missing – Up & Running Technologies, Tech How To's · February 24, 2023 at 4:12 pm
[…] Before you go bashing Microsoft, know that IBM actually created SMBv1. SMBv2 came out in 2006 and SMBv3, which is today’s standard, came out in 2012. However, the Computer Browser service was never updated to use these new more secure versions of SMB so you really shouldn’t be using it. It is dangerous in today’s world of sophisticated hackers. […]