Microsoft Windows Defender Application Guard was developed because so many tools were “sandboxing” that hackers were spending more and more time going under the security by attacking the operating system Kernel.
Application Guard operates as JUST less than a full virtual machine in something called a HyperV Container. These containers do NOT require Hyper-V to be installed but do require virtualization to be enabled in your computers BIOS.
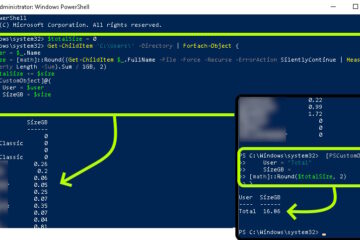
The slides below explain much of the technical detail but it boils down to Microsoft selected what they call their “Krypton” level of containerization for Application Guard. Containers virtualize the operating system and if you are having trouble imagining that, just think of them being independent virtual machines that share needed files from the base operating system.
In fact Krypton containers use a very cool function called Direct Map so that the container it builds is only 18MB in size and it copies files directly FROM the base operating system on demand. Other than what you as the admin specifies, it never copies files or data TO the base operating system.
It also uses what you can think of a dynamically expanding memory so that containers do not hog more RAM than needed at the time.
Once the container is called, it is displayed on the desktop using a very thin custom built RDP client that is very restricted to keep you safe. Until Application Guard was developed, Microsoft had always worked on the assumption that the server you were RDP’ing to was more safe than you. Application Guard required them to reengineer an RDP client based on the assumption that the server (i.e. container running your Edge browser) was hacked. Take a look at these slides for more details:
Don’t worry about your default settings from the original software you launched Application Guard from (i.e. Edge Browser), because when the container is built it copies your source settings into itself.




0 Comments