Most companies are worried about data exfiltration which is a fancy CTO / CISO way of saying data leaving your company. It used to be that most security and IT staff spent their days focusing nearly exclusively on hacks coming from outside the company, but today we see more and more internal hacks.
Through disgruntled employees, state actors having a hacker / spy get hired inside the company, or just good old stupidity, it is easy to have your valuable data wrongly taken outside of corporate control.
 One way to make it more difficult for people to exfiltrate data is to block write access to USB disks. Microsoft has made this retaliative easy to do through Group Policy or registry entries.
One way to make it more difficult for people to exfiltrate data is to block write access to USB disks. Microsoft has made this retaliative easy to do through Group Policy or registry entries.
Note that the this GPO or registry entry can be applied to the user instead of the machine, which might make it more palatable to some and more practical in the real world.
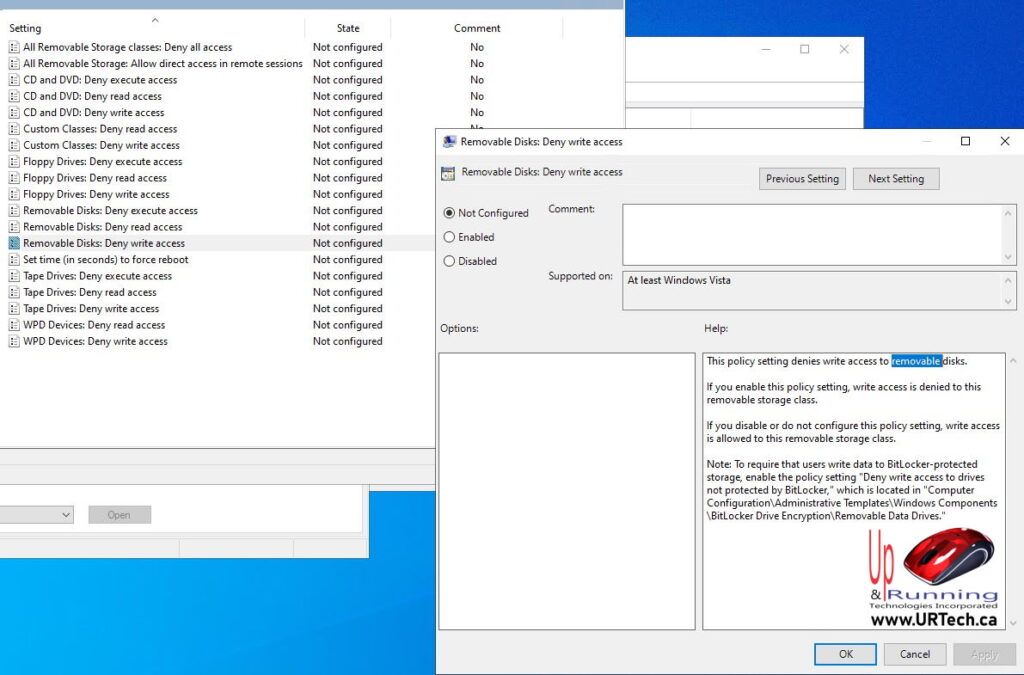
GPO To Block Write Access To USB Storage
The path to the Group Policy to disable write access to a USB drive is:
Computer Configuration or User Configuration > Policies > Administrative Templates > System > Removable Storage Access
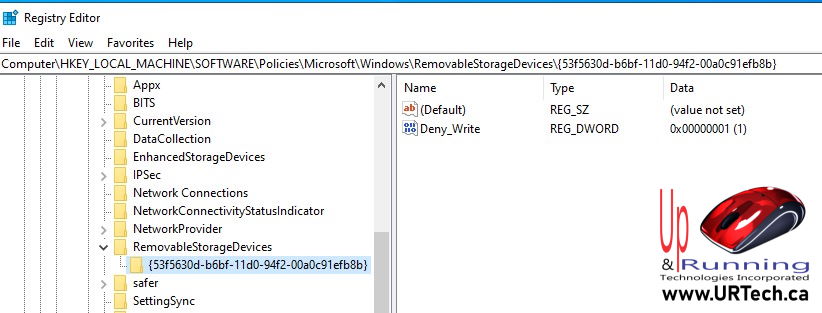
Registry To Block Write Access To USB Storage
The path to the Group Policy to disable write access to a USB drive is:
HKLM or HKCU > SOFTWARE > Policies > Microsoft > Windows >
RemovableStorageDevices
- If you don’t see a key named RemovableStorageDevices , you will have to create it
- Right click and create a NEW KEY named {53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
- Set is as a DWORD with a value of 1
If you want to control read write or execute on other devices, here is the list of registry entries.
For example, if you want to block read access to USB sticks or drives then you would set
HKLM or HKCU > SOFTWARE > Policies > Microsoft > Windows > RemovableStorageDevices > {53f5630d-b6bf-11d0-94f2-00a0c91efb8b} = 1
| Policy name | Device Class GUID | Registry parameter name |
| Floppy Drives: Deny read access |
{53f56311-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Read |
| Floppy Drives: Deny write access |
{53f56311-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Write |
| CD and DVD: Deny read access |
{53f56308-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Read |
| CD and DVD: Deny write access |
{53f56308-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Write |
| Removable Disks: Deny read access |
{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Read |
| Removable Disks: Deny write access |
{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Write |
| Tape Drives: Deny read access |
{53f5630b-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Read |
| Tape Drives: Deny write access |
{53f5630b-b6bf-11d0-94f2-00a0c91efb8b} | Deny_Write |
| WPD Devices: Deny read access |
{6AC27878-A6FA-4155-BA85-F98F491D4F33} {F33FDC04-D1AC-4E8E-9A30-19BBD4B108AE} |
Deny_Read |
| WPD Devices: Deny write access |
{6AC27878-A6FA-4155-BA85-F98F491D4F33} {F33FDC04-D1AC-4E8E-9A30-19BBD4B108AE} |
Deny_Write |
These changes will take effect as soon as the Group Policy of registry entries are on the computer. There is no need to reboot if you run a GPUPATE /FORCE.
If a device is already connected, it will continue to work until it is removed and plugged back in, so you don’t need to worry about corrupting data being transferred when the policy comes into effect.

0 Comments