Dell Endpoint Security Suite (ESSE and ESS) looks like a fantastic product I was very excited to play with it. ESSE should not be confused with your ordinary security tools, or perhaps it should, because it includes most of them.
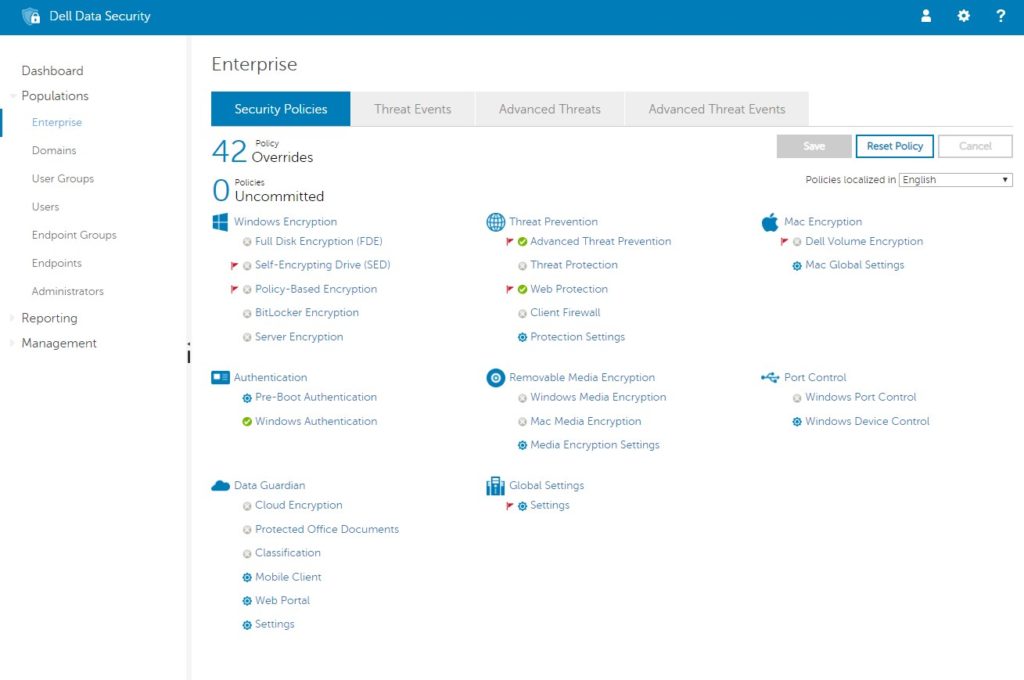
Dell ESSE provides:
- An awesome encryption suite that includes everything from Full Disk Encryption to Bit Locker management and ‘removable media’ encryption. As a differentiator, ESS offers Policy Based Encryption so you can apply encryption only to certain types or categories of files which is very cool.
- ATP – Advanced Threat Protection, what we call Signatureless Next Generation AntiVirus. ATP looks at the characteristics of a file and determines the likelyhood of it being malware.
- Threat Protection – a.k.a. good old signature based antivirus
- Web Protection – is an interesting customizable web filter to block access to a myriad of site types including, known phishing sites, gambling sites, anonymizers, social media sites…
- Desktop Firewall – a.k.a firewall
- Port Control – this lets you disable or enable USB ports or control the devices that are connected to your corporate PC’s
All of these products work on Windows Server and Desktop and encryption will also work on Mac’s.
Dell ESS is an ‘ingredient brand’ meaning that its modules are from different, highly regarded, companies. Those modules are tried and tested in both small business and global enterprises:
- ATP is Cylance
- Threat Protection is McAfee Enterprise
- Web Protection is McAfee
- Encryption is from Dell themselves
This is a very impressive list that provides nearly every layers of today’s ‘security onion’ on the desktop.
Note that Dell does not hide the fact that they are bundling other companies products. There are several places the Cylance logo prominently appears and McAfee is nearly as visible as it is if you purchased it directly.
The management interface is quick to respond and easy to understand after a 5 minute primer by Dells friendly staff.
As if all of that wasn’t enough Dell really wants this product to sell so they offer it a competitive price and are not afraid to deep discount that.
So what’s not to like about Dell ESS? Unfortunately, quite a lot:

- The desktop client does not provide a way (i.e. a popup) for users to see what was blocked or why which means they can work in circles for hours trying to guess why something is failing.
- The backend management console can (and regularly does) take an hour or more to show events from the clients. Combined with the desktop client not showing what is happening, a tech can spend a long time with an increasingly angry staffer looking stupid because he does not know the ESS is blocking something.
- Email alerts when malware or problems are found is a critical and common feature of all security systems so alerts should be easy to configure and be highly reliable. Unfortunately alerts are problematic in ESS. To get email alerts configured we needed to A – make cryptic entries on text file on the server using VI (yes the 1970’s are back and just as hard to use!) B – make a change in the server GUI C – make changes in the management console. After working with support on three occasions and a highly skilled dedicated Dell tech trying to save the sale, the most we could get was a daily email about the server status itself but no malware alerts.
- Web Protection blocks In-Private Browsing and you can not change that.
- If you are using Web Protection but not Threat Protection (McAfee), the Windows Security Center will have a red X on it indicating to your staff that something is wrong. As a result you have to teach your staff to ignore security warnings… not a good idea.
- The Dell ESSE management console does not include all of the features as the underlying technology from Cylance or McAfee BUT the event logs are written by Cylance or McAfee so the logs often point to things that do not exist in the Dell ESS console. This makes it incredibly difficult to troubleshoot.
- Because ESS was originally written as Dell’s encryption software and then the other modules added in, you must install the encryption module even if you are not using it.
- The desktop client installation and future upgrade process is far from straight forward. Dell’s preferred method is to download their master installer, then extract all of the files, then install each ‘module’ separately and with each products own custom switches.
- Upgrades to the Dell ESSE desktop agent require reboots. You may this is normal but Carbon Black Defense does not require reboots for most of its upgrades.
- The management server has to be installed on prem. In a world of SAAS, Dell’s local install is acceptable but soon to be an archaic way of running systems. On the bright side Dell offers the backend server in either a Windows VM or a Linux based “virtual appliance” that is easy to configure.
- Because the server is on-prem, remote PC’s (think field staff or travelers) have to either VPN into your company to get updates or you have to poke holes in your firewall to accommodate the communication. This is just one more needless step that reduces your security.
- If you are logged into the ESSE management console, then close your browser and even reboot your PC, the next time you attempt to sign in (say 5 days later) it will say “You Have Been Logged Off Due To Inactivity” so you have to log in twice to get connected. This is not a crisis but when it happens every single time, it starts to get under your skin.
- Several minor settings just don’t seem to work. For instance in ATP there is a setting for DEFAULT BROWSER that did nothing in our tests. You may think these are just misconfiguration issues, but ESS support could not figure out what we were doing wrong either.
- Several critical settings cannot be altered after their initial configuration. For instance, if you add tech as a console user and 2 months later that tech changes jobs to something outside of IT, you will want to remove him from ESS… but you can’t. Once a user is added the only way to get rid of them is by deleting them from Active Directory. Also, once a domain is added it can not be deleted and that is a serious problem if you have multiple domains and you started your testing on just one of those domains.
- More than a few times we would see ESS block some file but not log anything in the ESS management console. We could only prove the problems were caused by ESS by uninstalling it and trying again. We would talk to support about it and they would ‘hum and ha’ but in the end if we wanted to track down the problem, we had to collect logs, send them into Dell and wait days for them to analyse them. At this point you have already been fired so you don’t care.
- If you want to use Web Protection there is no way to whitelist URL’s. You can only whitelist IP addresses. That just won’t work if you are hosting sites with global players like Amazon AWS or Microsoft O365 (think about your SharePoint and Teams sites). That is just nutty. When we asked our find sales contact to ask the ESS dev group about this we were told they responded with “this is not on next years road map”.
- We found the reporting to be almost useless because it either did not contain the information we wanted.
- After several partial days of effort and 3+ hours with ESSE technical support over two different days, we could not encryption to work at all. Our encryption tech knows what he is doing with encryption and the Dell ESS management console looks complete and logical… but in the end we gave up.
- Several of the logs shown in the ESS management console are missing fields we think of as core… like date fields.
- …and just to top this off Blackberry just bought Cylance so the relationship with Dell may get pulled or strained, or it might improve, who knows. Companies hate uncertainty.
There were a myriad of much smaller issues (like the usual quality problems with first level support staff, it does not appear on the Gartner Magic Quadrant, we could not find ESS reviews…) but I really don’t want to give you the impression that we did not like the product. We LOVED Endpoint Security Suite Enterprise (ESSE) because:
- it got top marks from my ‘zero day’ testing in which I sent hundreds of pieces of new malware to it (Among others, I use testmyav.com for zero day testing)
- it is pretty
- it is thoughtfully constructed and logical
- it demo’s beautifully
- second and third level tech support is very good
The problem is ESS did not love us and that caused me to hold out hope for this product more than any other security product I have tested in the last 25 years.
In the end we had to walk away from Dell ESS. Have I mentioned how much this frustrates me?!?!?



0 Comments