The title of this article might seem a bit convoluted but this article will explain how to troubleshoot Azure AD Sync failures.
In our case we have a client that was making a lot of changes on their on premise active directory and then found that new accounts created on-prem were not syncing to M365 or Azure AD.
We launched the synchronization service manager on the azure ad connect server and found three odd things:
- Under inbound synchronization there was something called Projections which we did not understand
- on those projections we found error “sync-generic-failure“
- we noticed a status of “stopped-deletion-threshold-exceeded“
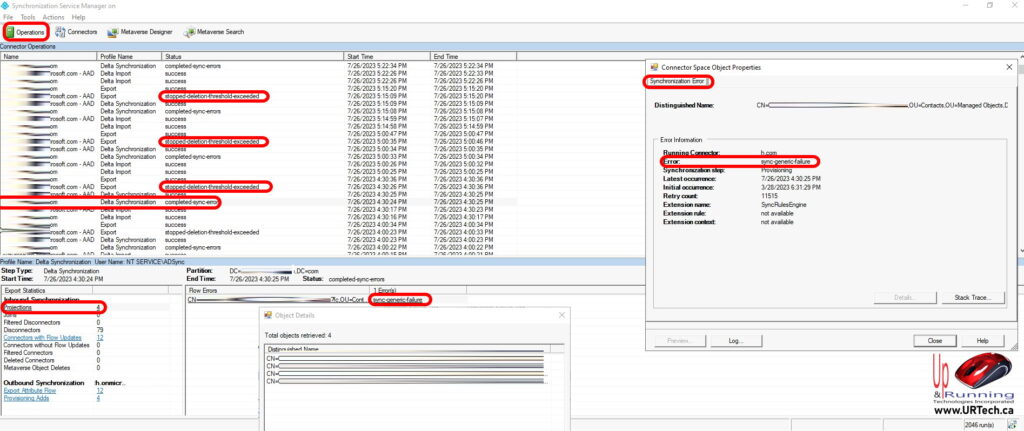
In our case the problem was hinted at by “stopped-deletion-threshold-exceeded” even though our problem as ADDING new accounts.
The problem turned out to be that various people had deleted hundreds of accounts from the on Prem Active Directory. Azure AD Sync Has a security feature to prevent accidental deletions that kicks in when more than 500 accounts have been deleted. Yes this stopped deletion threshold actually blocked syncing of new accounts as well, even though the errors an documentation we read did not mention this.
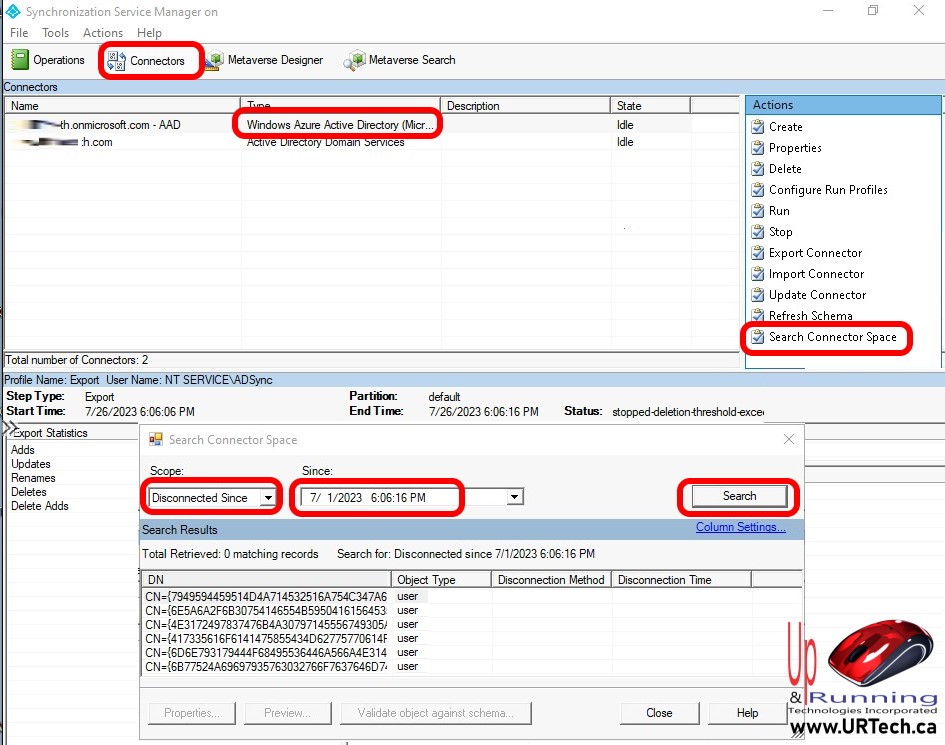
To confirm that this is your problem:
- launch Synchronization Service Manager
- click Connectors button (at the top)
- click on the connector entry that has a Type of Windows Azure Active Directory
- click Search Connector Space (actions pane on the far right)
- change the Scope drop down to Disconnected Since
- set the Since field to a few days BEFORE the problem was noticed
- click the Search button
If you notice a substantial number of entries that have not synced well that’s your problem just like it was ours:
In our client situation one of the technicians was being particularly security conscious and actually lowered the default number of deletions from 500 down to 100. This meant that if we had more than 100 deletions in a single half an hour cycle that Azure Active Directory Sync would intentionally fail.
A curiosity about this is that we found password changes did continue to sync, it was just the addition of new accounts and the deletion of old accounts that were affected.
The solution is to disable the threshold, force a sync, wait a few minutes and then turn the threshold back on and that as you can see in the screen shot below is exactly what we did
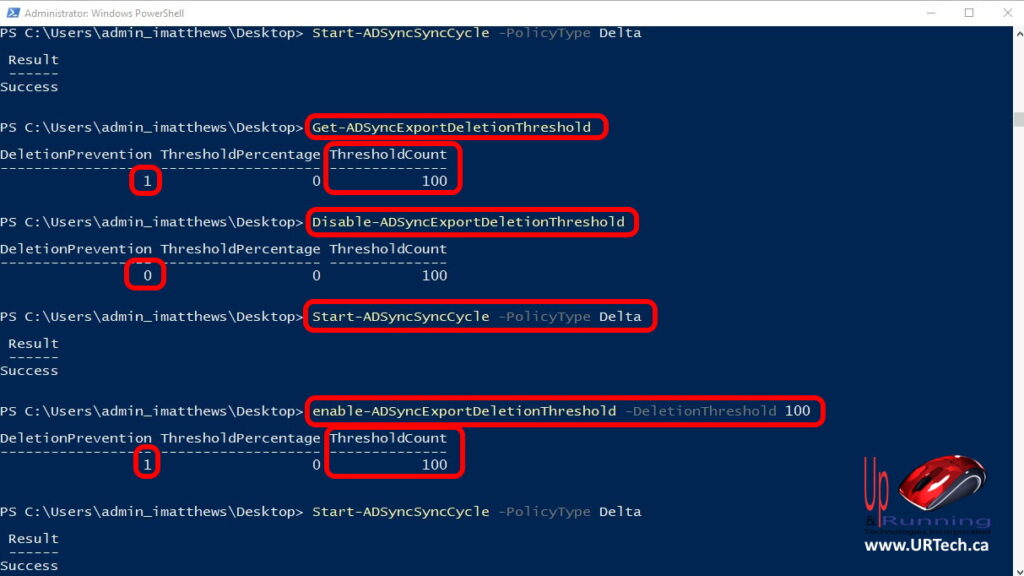
- Open a PowerShell as an Administrator, on the server with Azure AD Sync installed
- To find out what your deletion threshold is, enter
Get-ADSyncExportDeletionThresholdand press Enter - To disable the Azure deletion limitation, enter
Disable-ADSyncExportDeletionThresholdand press Enter - To force a sync, enter
Start-ADSyncSyncCycle -PolicyType Deltaand press Enter - Wait a few minutes and then check your Azure Active Directory or Microsoft 365 to see if the old accounts are gone and the new ones are created
- To reenable the Azure AD Sync deletion limitation, enter
Enable-ADSyncExportDeletionThreshold -DeletionThreshold 500and press Enter- Note that in our case shown the screenshot, we se the threshold back to 100, but 500 is the default
- Have a nice day!


0 Comments