Today we had a good question from a frustrated client. One of their users had their laptop stolen so the administrator logged into Microsoft 365 / Azure and disabled their account. About an hour or later the user came into the office picked up a loner laptop and was able to sign into it using the credentials that the administrator had disabled a short while earlier.
The administrator wanted to know how someone could sign in when an account was deactivated and the answer is pretty straightforward:
This company, like most companies these days, is using Azure AD Sync which Synchronizes they are on-premise Active Directory to the Microsoft 365 / Azure Cloud. Again just like most companies, they were using a one-way sync from their on-prem Active Directory to the Microsoft cloud. By default that Azure AD Sync occurs every 30 minutes which means if you make a change to an account that is in your on-prem AD, it will be undone in less than 30 minutes.
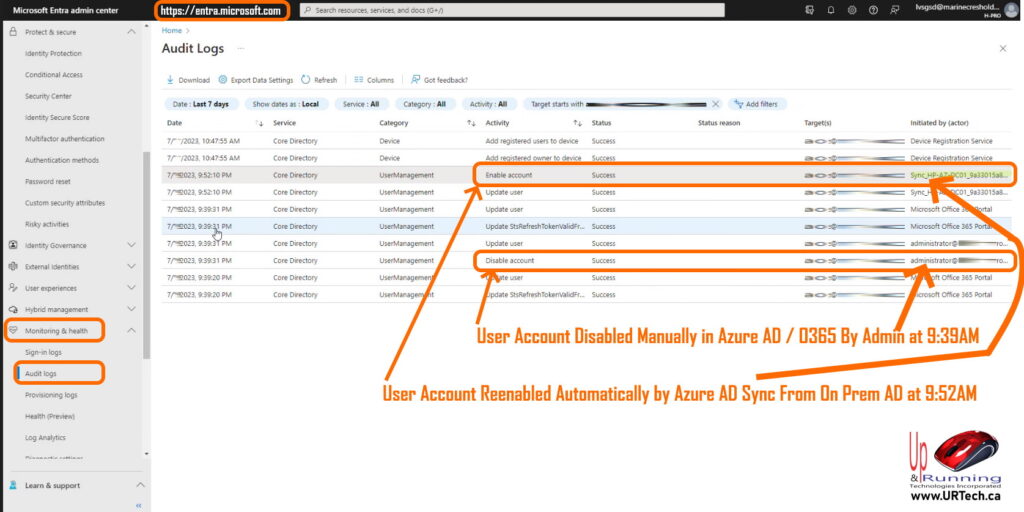
If you want to see if this was your situation use the new Microsoft Entra (formerly Microsoft Identity Services) cloud console:
- Surf to https://entra.microsoft.com
- Click SHOW ALL in the menu on the left
- Click MONITORING & HEALTH
- Click AUDIT LOGS
- Look for who initiated your DISABLE ACCOUNT activity
- Look to see if SYNC-XXXXX initiated the ENABLE ACCOUNT activitity


0 Comments