Yesterday we were troubleshooting an error we found in our server monitoring tools that uses WMI queries to detect problems. It was reporting:
File Server Errors LogonThe host {Server} is now in state warn as it has 1.2067 logon errors per second. This could indicate a password cracking attempt.
The problem is that servers Event Viewer logged no log on issues. After some research we found that our monitoring tool (Logic Monitor) was using this WMI Query:
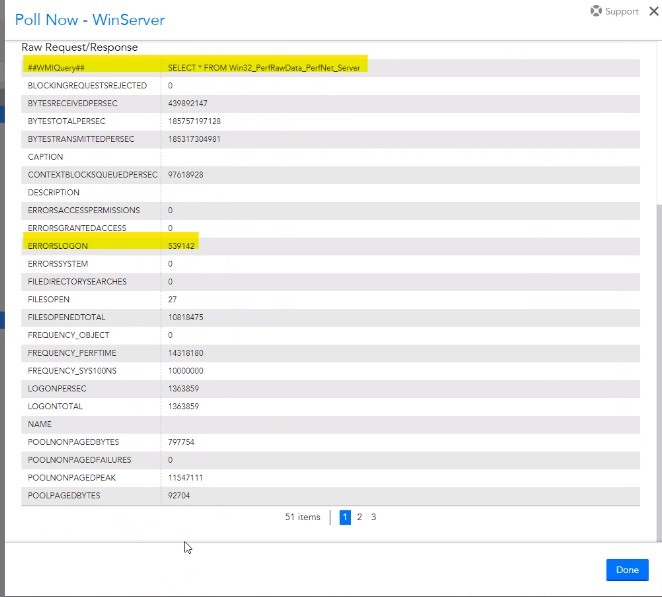
SELECT * FROM Win32_PerfRawData_PerfNet_Server
and was specifically reporting on the ERRORSLOGON counter. That word COUNTER is the key. WMI was not recording details like, which user or which machine the errors were coming from; WMI was just counting the failures.
We decided to run a few queries of our own to get more details:
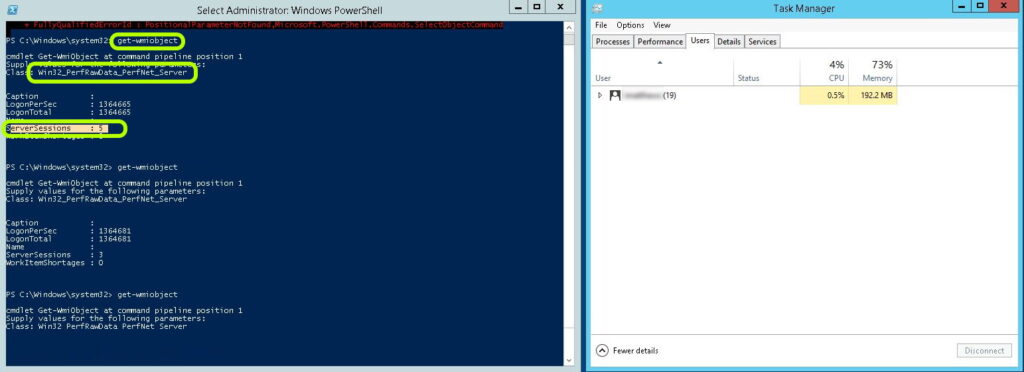
- Launch a PowerShell as an Admin
- Type
get-wmiobjectand press ENTER - Type
Win32_PerfRawData_PerfNet_Serverand press ENTER
We noticed the SERVERSESSIONS and decided to check if any other admins were logged into this server. We launched TASK MANAGER and found 7 other admins have left themselves logged in but were now DISCONNECTED. I right clicked on each one of them and selected LOGOFF. Within a minute, Logic Monitor stopped reporting the failed logon attempts.
My guess is that someones account expired or they changed their AD password on a different machine but were still logged in on this machine. Remember that just because an RDP session is DISCONNECTED does NOT mean that the connections and apps they launched previously are not still running and could cause this very problem.



0 Comments