WHAT IS KERBEROS AUTHENTICATION IN WINDOWS?
Microsoft Windows Active Directory has a few fundamental core components that everything else is built upon. One of those is the main Kerberos key. The KRBTGT (Kerberos Ticket Generating Ticket Account) user account (take a look in ADUC > USERS… it is there), is used to encrypt and digitally sign all Kerberos tickets… which is ALL of the users and ALL of the devices.
“…Kerberos is an authentication protocol that is used to verify the identity of a user or host.
The Windows Server operating systems implement the Kerberos version 5 authentication protocol and extensions for public key authentication, transporting authorization data, and delegation…
The Kerberos Key Distribution Center (KDC) is integrated with other Windows Server security services that run on the domain controller. The KDC uses the domain’s Active Directory Domain Services database as its security account database…”
SOURCE
WHAT IS A GOLDEN TICKET ATTACK?
Because the KRBTGT user (almost) never changes its key and that key is… well… the key to unlocking all encrypted user and device communication on your network, an even moderately sophisticated hacker that had domain admin access to your network, likely copied that key. It is the Golden Ticket to all the Active Directory goodies.
So if someone had domain admin access on your network, you really need to change that ticket. This is why many security experts say it is advisable to change your domains Golden Ticket on a regular schedule.
HOW CAN THE GOLDEN TICKET BE CHANGED?
This is a slightly more tricky question than you might have anticipated. Changing the Golden Ticket does not invalidate the original; it just adds another Golden Ticket and that will not keep you safe.
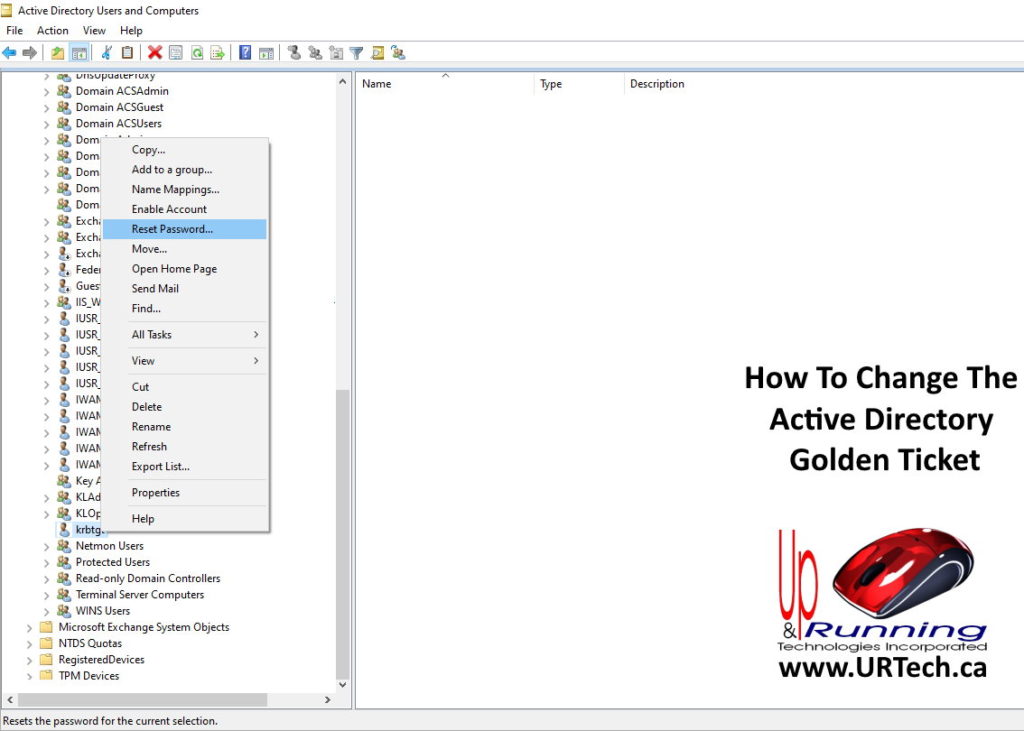
Change the Password on the KRBTGT Account
Simply using Active Directory Users and Computers, you can expand USERS, right click on KRBTGT and change its password. That will expire the old Golden Ticket and does not even require a reboot!
Change the Active Directory Functional Level
One way to change the Golden Ticket is to change the Domain Functional Level. Many companies fail to upgrade the functional level as new versions come out so it is not unusual to see a SERVER 2008 or even 2003 Domain Functional Level on otherwise current Windows networks.
To see what version your network is running just open ACTIVE DIRECTORY DOMAINS AND TRUSTS and click ACTION > RAID FOREST FUNCTION LEVEL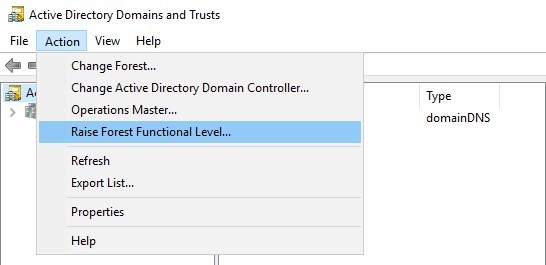 Note that it says RAISE not CHANGE. This is because there is no (easy) way to reduce the functional level after it has been upgraded.
Note that it says RAISE not CHANGE. This is because there is no (easy) way to reduce the functional level after it has been upgraded.
Upgrading the Active Directory Function Level generally tightens up the core security on the network but most techs and most companies will not even notice it. The process will only take a few seconds.
If you want to know the details of what actually changes skim through THIS short Microsoft article.
I have recently confirmed with Microsoft support that changing the AD Functional Level will add a new Golden Ticket but the old one will still work until it expires. In other words, you should raise the Functional Level but it won’t solve your hacker problem.

2 Comments
SOLVED: How Long Can A Domain Controller Be Offline? – Up & Running Technologies, Tech How To's · May 9, 2022 at 4:07 pm
[…] Tombstone Lifetime can be set manually, but by default is is set by the first Domain Controller that is added to creat the […]
Active Directory Kerberos Gold Ticket Exploit - DETECTX | Cloud Security Expert · February 24, 2021 at 7:40 pm
[…] https://www.urtech.ca/2020/07/what-is-an-active-directory-kerberos-golden-ticket-how-can-it-be-easil… […]