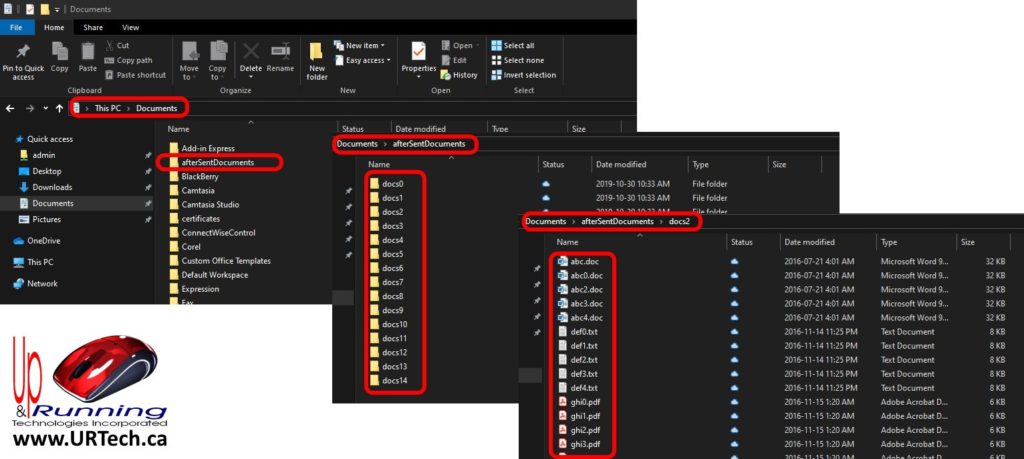
If you see a folder named “afterSentDocuments” in your Documents folder it might cause some concern because no human intentionally added that. It turns out that that folder and files are the ‘honey pot’ for excellent corporate security software named SentinelOne.
After talking to a pile of vendors including Microsoft, SentinalOne told me:
They’re our Malware/Ransomware decoys!
The SentinelOne Agent Installer installs a number of files on the endpoint. Most of these files are directly related to product functionality, but some are used to assist with detections. A handful of these files are called decoys. These files are planted on the system in user accessible locations in order to act as a honeypot for malware and ransomware. These files are monitored by the SentinelOne Agent for modification, deletion, and encryption that could indicate an attack.
Some of the locations of these files are:
C:\Users\Public\Documents\afterSentDocuments
C:\Users\Public\appdata\local\afterSentDocuments
C:\Users\Default\Documents\afterSentDocuments
C:\Users\(each users folder)\Documents\afterSentDocumentsThe locations listed above contain additional folders and files that are hidden but accessible without special permissions. The files themselves are harmless but play an integral part in ransomware detections. Deleting these files somewhat reduces the chance some ransomware activities can be identified, so it is best to leave the files as they are.
9 Comments
Everette Fevold · February 21, 2024 at 10:42 pm
Tremendous guide! This explained it easily for me. Thanks!
Florine Buchna · December 23, 2023 at 1:12 pm
And Im running from a standard users account with strict limitations, which I think may be the limiting factor, but Im running the cmd as the system I am currently working on.
Magda Yzaguirre · November 21, 2023 at 2:05 am
It’s super helpful, I was really like Sentinal One
uptoWord · October 22, 2022 at 3:38 am
I’m not sure what the afterSentDocuments folder and files are, but I’m looking forward to learning more about them!
Catherine · March 12, 2022 at 2:20 pm
Found the same aftersent documents folder and it has like a written story yet the sentences make no sense. Is this what is supposed to happen?
Ian Matthews · April 4, 2022 at 6:05 pm
Yes, they are decoy docs that are being monitored by SentinelOne. They are looking to detect attempted encryptions and deletions.
Finoquio · October 6, 2021 at 2:09 am
Thank you very much
Mike Renna · March 5, 2020 at 3:59 am
Thanks for explaining this! But how long till ransomware starts excluding these folder locations / these file names. Just like they exclude windows operating files?
I just started using S1 on client machines. Just like they pitch that comparing malware against signatures is not viable anymore, having static names of folders, files and fixed text inside them seems to not be viable.
Ian Matthews · March 13, 2020 at 12:22 pm
Hi Mike;
I have certainly had the same thought. I expected S1 to change the name of those files and folders periodically, but apparently they do not.